- If the outputs from the two systems are similar, confidence in the ICT systems.
- Users have time to familiarize themselves with the ICT systems.
- It is reliable because it enables thorough testing.
- Weaknesses in either of the systems are corrected.
Kavungya answered the question on June 5, 2019 at 11:38
- Differentiate between a modem and a multiplexer.(Solved)
Differentiate between a modem and a multiplexer.
Date posted: June 5, 2019. Answers (1)
- Distinguish between bounded and unbounded transmission media, giving two examples in each.(Solved)
Distinguish between bounded and unbounded transmission media, giving two examples in each.
Date posted: June 5, 2019. Answers (1)
- 1.(i) Define Twisted pair cables.
(ii) Outline the two types of twisted pain cables.(Solved)
1.(i) Define Twisted pair cables.
(ii) Outline the two types of twisted pain cables.
Date posted: June 5, 2019. Answers (1)
- Define Coaxial cables and give examples of such cables.(Solved)
Define Coaxial cables and give examples of such cables.
Date posted: June 5, 2019. Answers (1)
- List two advantages of cell phones over fixed lines.(Solved)
List two advantages of cell phones over fixed lines.
Date posted: June 5, 2019. Answers (1)
- Write in full hence, explain the term ICT.(Solved)
Write in full hence, explain the term ICT.
Date posted: June 5, 2019. Answers (1)
- Name the type of processing that would be required by a payroll system.(Solved)
Name the type of processing that would be required by a payroll system.
Date posted: June 5, 2019. Answers (1)
- State four components of an electronic Point-of-sale terminal.(Solved)
State four components of an electronic Point-of-sale terminal.
Date posted: June 5, 2019. Answers (1)
- State the functions of I/O devices(Solved)
State the functions of I/O devices
Date posted: June 5, 2019. Answers (1)
- Give the ways of controlling carelessness as a threat to the safety of computer system.(Solved)
Give the ways of controlling carelessness as a threat to the safety of computer system.
Date posted: June 5, 2019. Answers (1)
- Give the ways of controlling Vandalism.(Solved)
Give the ways of controlling Vandalism.
Date posted: June 5, 2019. Answers (1)
- State the ways of controlling White- collar crime.(Solved)
State the ways of controlling White- collar crime.
Date posted: June 5, 2019. Answers (1)
- Explain the term nibbles as used in data representation in computers(Solved)
Explain the term nibbles as used in data representation in computers
Date posted: June 5, 2019. Answers (1)
- What is 1001011.011 – 111.111 ?(Solved)
What is 1001011.011 – 111.111 ?
Date posted: June 5, 2019. Answers (1)
- What is 1110.0111 + 1101001.11 ?(Solved)
What is 1110.0111 + 1101001.11 ?
Date posted: June 5, 2019. Answers (1)
- Distinguish between machine and assembly language(Solved)
Distinguish between machine and assembly language
Date posted: June 5, 2019. Answers (1)
- State the type of translator necessary for a program written in:
(i) High level language
(ii) Assembly language(Solved)
State the type of translator necessary for a program written in:
(i) High level language
(ii) Assembly language
Date posted: June 5, 2019. Answers (1)
- Briefly explain the purpose of the following types of program documentation:
(a) User manual
(b) Reference guide
(c) Quick reference guide(Solved)
Briefly explain the purpose of the following types of program documentation:
(a) User manual
(b) Reference guide
(c) Quick reference guide
Date posted: June 5, 2019. Answers (1)
- Consider the entries made in the cells below
State the value displayed in cell C13.(Solved)
Consider the entries made in the cells below
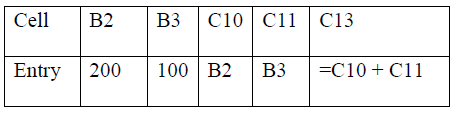
State the value displayed in cell C13.
Date posted: June 5, 2019. Answers (1)
- Distinguish between labels and formulae with respect to spreadsheets(Solved)
Distinguish between labels and formulae with respect to spreadsheets
Date posted: June 5, 2019. Answers (1)