
Intermediary devices interconnect end devices. These devices provide connectivity and work behind the scenes to ensure that data flows across the network. Intermediary devices connect the individual hosts to the network and can connect multiple individual networks to form an internetwork.
Examples of intermediary network devices are:
• switches and wireless access points (network access)
• routers (internetworking)
• firewalls (security).
• Hubs, switches, wireless access points, and other devices used for accessing the network, file servers, web servers, print servers, modems, devices using for internetworking such as routers, bridges, repeaters, and security firewalls, etc.
The management of data as it flows through the network is also a role of the intermediary device. These devices use the destination host address, in conjunction with information about the network interconnections, to determine the path that messages should take through the network.
Titany answered the question on November 30, 2021 at 11:16
- Explain two circumstances under which unshielded twisted pair (UTP) cables are most applicable in network installation(Solved)
Explain two circumstances under which unshielded twisted pair (UTP) cables are most applicable in network installation
Date posted: November 30, 2021. Answers (1)
- Outline two factors that should be considered when selecting an Internet bandwidth, other than cost(Solved)
Outline two factors that should be considered when selecting an Internet bandwidth, other than cost
Date posted: November 30, 2021. Answers (1)
- Data communication system should exhibit distinctive features. Explain two desirable features that could be exhibited by the system(Solved)
Data communication system should exhibit distinctive features. Explain two desirable features that could be exhibited by the system
Date posted: November 30, 2021. Answers (1)
- Define the term node as applied in data transmission(Solved)
Define the term node as applied in data transmission
Date posted: November 30, 2021. Answers (1)
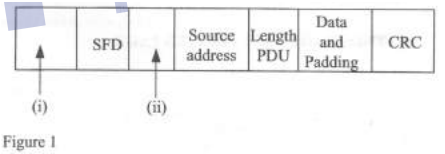
- Figure 2 shows a typical tool bar of a browser program. Outline the functions of
each of the tools labelled (i), (ii), (iii) and (iv)
(Solved)
Figure 2 shows a typical tool bar of a browser program. Outline the functions of
each of the tools labelled (i), (ii), (iii) and (iv)
Date posted: November 30, 2021. Answers (1)
- Outline four roles of user agent as used in email software(Solved)
Outline four roles of user agent as used in email software
Date posted: November 30, 2021. Answers (1)
- Describe two modes of licensing for network software(Solved)
Describe two modes of licensing for network software
Date posted: November 30, 2021. Answers (1)
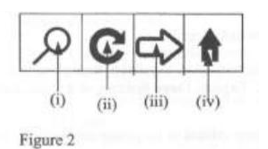
- Figure 1 shows an Ethernet frame. Outline the parts labelled(Solved)
Figure 1 shows an Ethernet frame. Outline the parts labelled
Date posted: November 30, 2021. Answers (1)
- Explain three circumstances that would necessitate the installation of a point-to-point protocol in corporate networks(Solved)
Explain three circumstances that would necessitate the installation of a point-to-point protocol in corporate networks
Date posted: November 30, 2021. Answers (1)
- Cloud computing is widely used in business firms. Explain two benefits that could be influencing the trend(Solved)
Cloud computing is widely used in business firms. Explain two benefits that could be influencing the trend
Date posted: November 30, 2021. Answers (1)
- Distinguish between channel B and channel D as used in integrated services digital network (ISDN)(Solved)
Distinguish between channel B and channel D as used in integrated services digital network (ISDN)
Date posted: November 30, 2021. Answers (1)
- Outline two applications of a CSMA/CD technology(Solved)
Outline two applications of a CSMA/CD technology
Date posted: November 30, 2021. Answers (1)
- Describe two classification of fiber optic cables(Solved)
Describe two classification of fiber optic cables
Date posted: November 30, 2021. Answers (1)
- TCP /IP is known for it capability to provide reliable transportation of data packets from the source to destination. Explain three features of the protocol...(Solved)
TCP /IP is known for it capability to provide reliable transportation of data packets from the source to destination. Explain three features of the protocol that promotes its reliable transport
Date posted: November 30, 2021. Answers (1)
- Explain three functions of data link layer(Solved)
Explain three functions of data link layer
Date posted: November 30, 2021. Answers (1)
- Routing protocols are critical in data transmission. Explain three functions that likely to be performed by these protocols(Solved)
Routing protocols are critical in data transmission. Explain three functions that likely to be performed by these protocols
Date posted: November 30, 2021. Answers (1)
- Differentiate between symmetric and asymmetric keys as used in network security(Solved)
Differentiate between symmetric and asymmetric keys as used in network security
Date posted: November 30, 2021. Answers (1)
- A good network design should produce a scalable network. Outline four ways of achieving this network objective(Solved)
A good network design should produce a scalable network. Outline four ways of achieving this network objective
Date posted: November 30, 2021. Answers (1)
- Explain three Internet services that could be utilized by students in technical institutions
(Solved)
Explain three Internet services that could be utilized by students in technical institutions
Date posted: November 30, 2021. Answers (1)
- Convert the digital encoded signal in (i) into on-return-to-zero (NRZ) line code(Solved)
Convert the digital encoded signal in (i) into on-return-to-zero (NRZ) line code
Date posted: November 30, 2021. Answers (1)